Google and Yahoo have both announced a new set of requirements that senders must meet from the beginning of February 2024 to ensure that their email is delivered to mailboxes on their services. Creating a DMARC record for your domain is key to proper domain security.
The long and short of these requirements are that domains should have both SPF and DKIM enabled for any domain that they’re sending email from. All domains should have this as a minimum anyway.
Your email provider should be able to tell you what to add for these two records.
If you’re using a third-party tool like SendGrid, they will also have instructions on managing these, often by an automated security mechanism. I have a handy article titled SendGrid Account Setup and Domain Verification with Azure DNS that will take you through this process from end to end.
The more important part of the new requirements is the need to have a DMARC record configured if you send more than 5000 emails a month to either Gmail or Yahoo services.
A DMARC record essentially tells the receiving server what to do if an email fails an SPF or DKIM check.
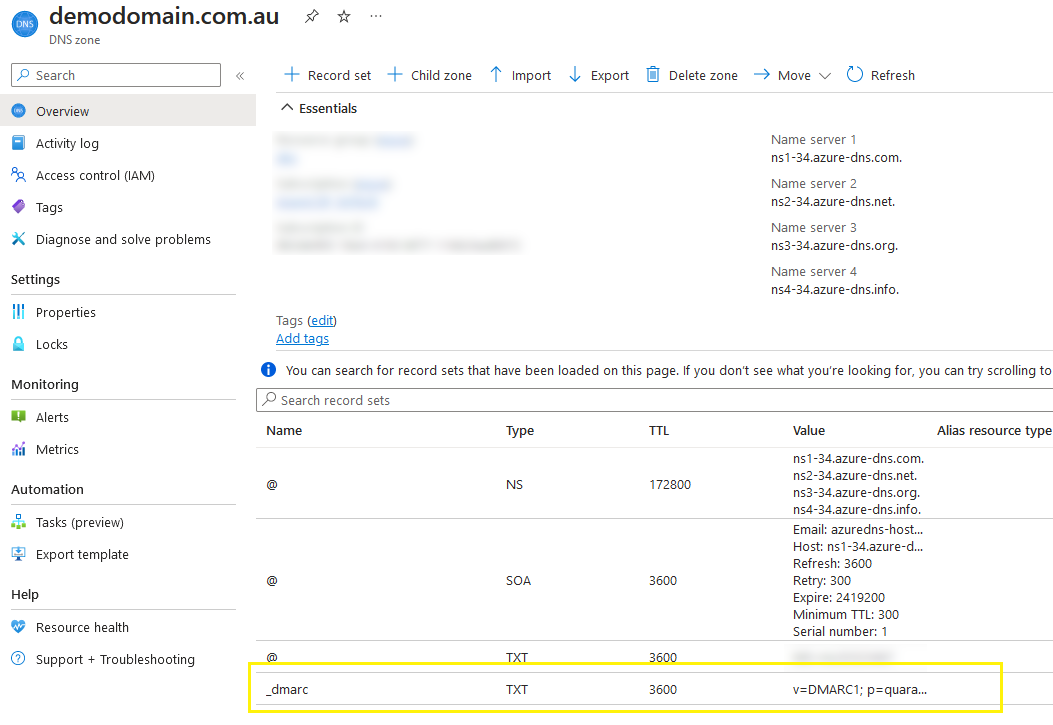
This would be set up as a TXT DNS record with the hostname of _dmarc, so would resolve as “_dmarc.domainname.com”
How to create a DMARC record for your domain
The most basic type of DMARC record would look like below
"v=DMARC1; p=none;"This is saying that any failures of SPF and DKIM should be ignored.
While this will satisfy the new requirements, it doesn’t really add to the security of your domain in any way.
If you want to add the extra level of security, or if your domain is being subjected to spoofing regularly, you can move the policy “p” value to “quarantine”
"v=DMARC1; p=quarantine;"This will tell the receiving server to quarantine, or send the email to the Junk Mail folder if it looks suspect or fails the SPF or DKIM checks
You can also set the policy to “reject”.
"v=DMARC1; p=reject;"You should only set the policy to reject if you’re an experienced postmaster and understand the implications on deliverability.
You should also include the “rua” setting in your DMARC record as well. This allows DMARC reports to be sent to you for messages that are classed as unqualified (failing SPF or DKIM). This “rua” setting should be the email address of whomever manages email for your domain (prefixed with “mailto:”)
"v=DMARC1; p=quarantine; rua=mailto:admin@mydomain.com"If you were using Azure DNS, your record would look like the following
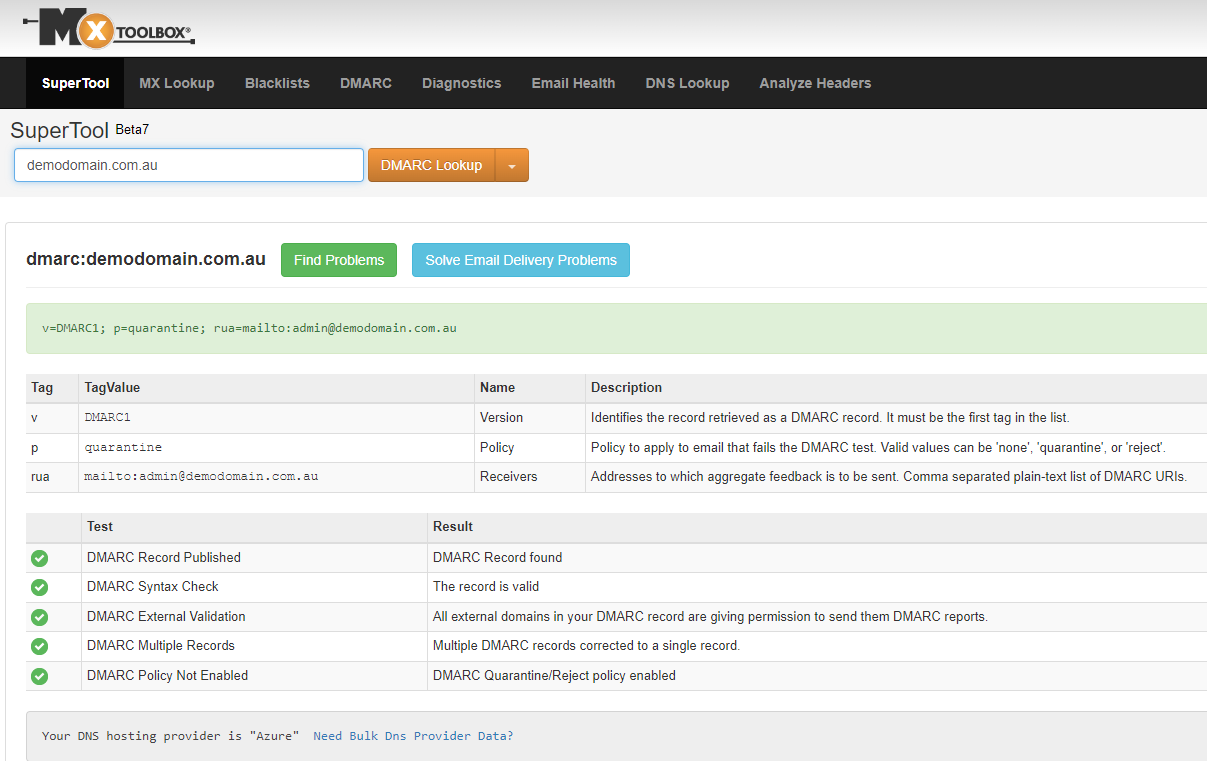
Once you’ve added this record, you can use a tool like MXToolbox to verify the record.
You can also use tools like Google Postmaster to manage your email and see any spam reports or deliverability issues.
If you’d like to read more about DNS, check out my DNS article list
SendGrid also have a number of great articles on the new requirements and DMARC in general:

